In my previous post I explained what happens when you use your browser to access a HTTP site. However, almost all traffic in the internet nowadays is performed over HTTPS. So what exactly does that mean and how does it differ from the HTTP example?
Again, we will utilize our trusted carrier pigeon to transport our data. After all, why would you use anything else if you were able to use carrier pigeons. Just look at it.

To be honest, you might want to use something else but carrier pigeons, due to the latency issues that have been observed. But I like pigeons, so we will use pigeons.
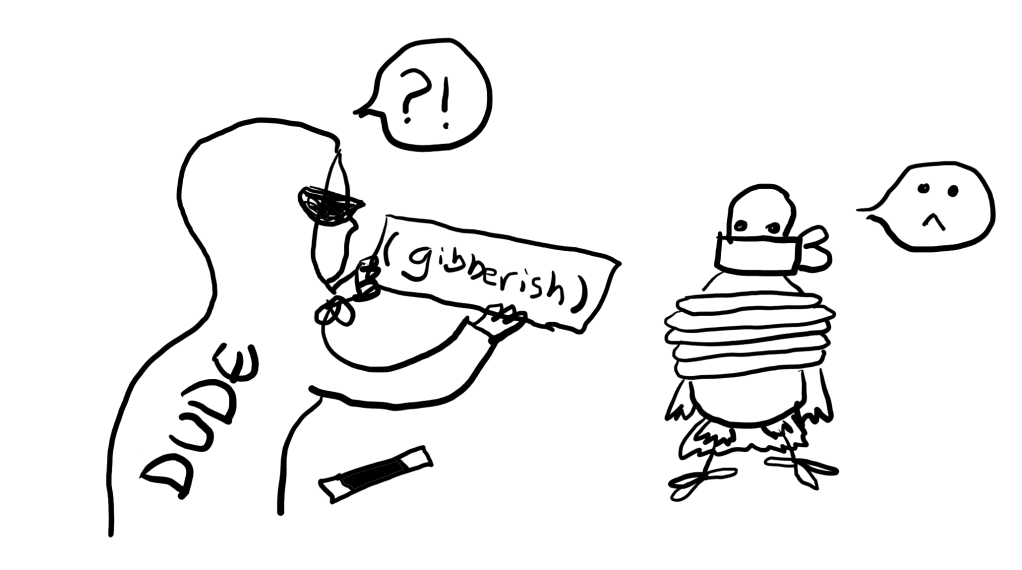
Let us begin by considering what is wrong with plaintext HTTP. Here we have our pigeon transporting a HTTP request from the client to the server. We are trying to login to a web page, so our request includes our username and password.

Oh no, our pigeon was caught! A dude was hiding in the bushes with a net, and caught our pigeon.
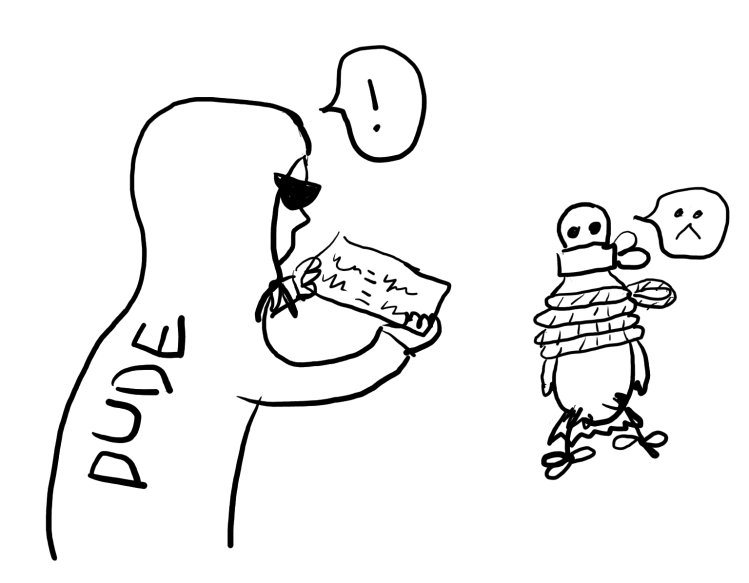
Now they have our credentials, and can do whatever they want with them. And we will have no clue that someone has seen our credentials – the dude will let our pigeon go after reading the message, and the pigeon will continue its way to the server.
If only there was a way that prevented the dude from getting our credentials, even if they were able to catch our pigeon on the way… Yes, that is HTTPS.
So, we want to be able to communicate with the server so that even if someone happens to see our messages on the way, they will not understand what we are talking about. We will need to use encryption. Encryption deserves an entire blog post devoted to it, so this time we will just simplify things. We will use a magic wand.
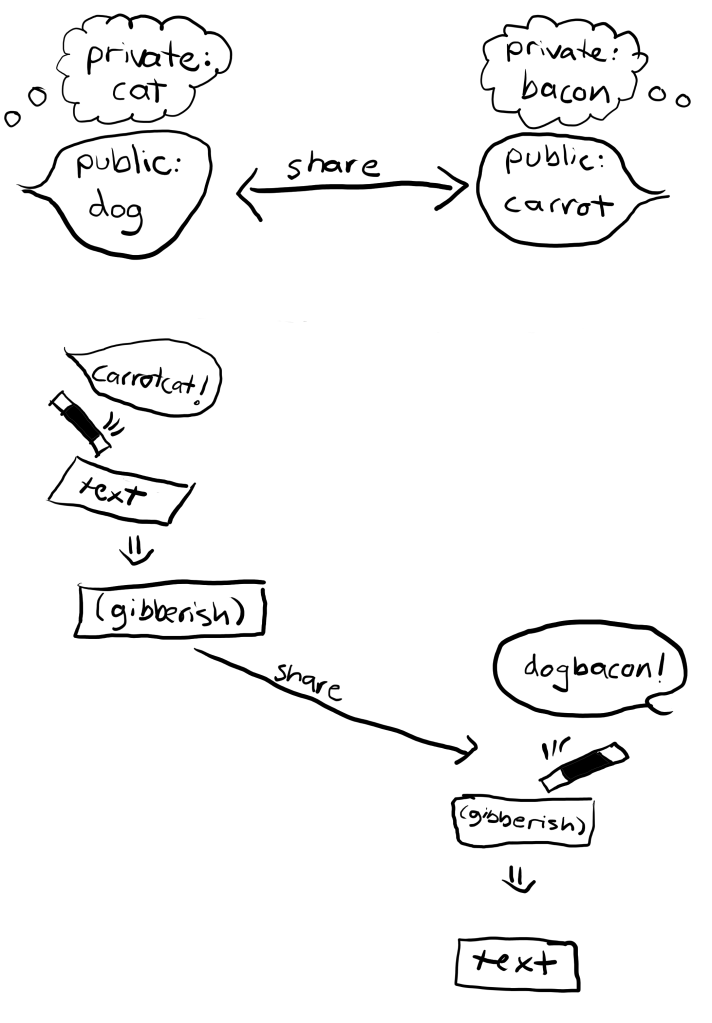
Our magic wand can be used for turning text into gibberish and back to normal. However, not everyone who has a similar magic wand can turn every gibberish message back to normal. As any cool magic trick, for it to work, you need to know the magic words!

Our magic wand needs two magic words. We have one word, which we can tell anyone. Let us call this word our public key. And we have another word, that we will want to keep to ourselves. This one we call our private key.
If we know someone else’s public key (as said, anyone can know your public key), we can combine that with our private key. When we tap a message, which we want to send, with our magic wand, and say this combined word aloud, the message turns into gibberish. And the coolest part is that when we let the other person know our public key, they can combine our public key with their own private key. By using this combined word when tapping the gibberish message with their magic wand, they can turn the gibberish back into the original text!
Great, we have an encryption method! We can now initiate a secure connection with the server. However we have never spoken with the server before, so we cannot just start sending gibberish to it. We will begin by letting the server know that we would like to start a secure connection with it, and we have this cool wand.

We had luck: the server happens to have a similar wand as we do. The server sends a reply back saying that it would also like to start a secure connection, and that it happens to have the same kind of wand. It also includes its public key, “rain”, with the message. And finally, it attaches a certificate with the message, to prove to us that we really are talking to the server that we want to talk to.
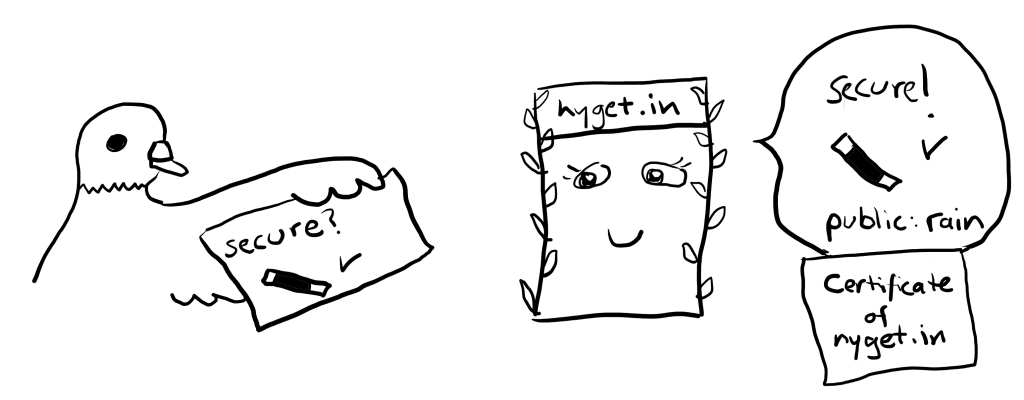
We take a look at the certificate. It checks out: we trust the company that has given this certificate to the server, and we can see that the certificate is not fake. Great! (Side note: this is represented in most browsers with a lock symbol next to the URL!) Now we have everything we need to send the server the same login request we sent before, but this time it will be secured!
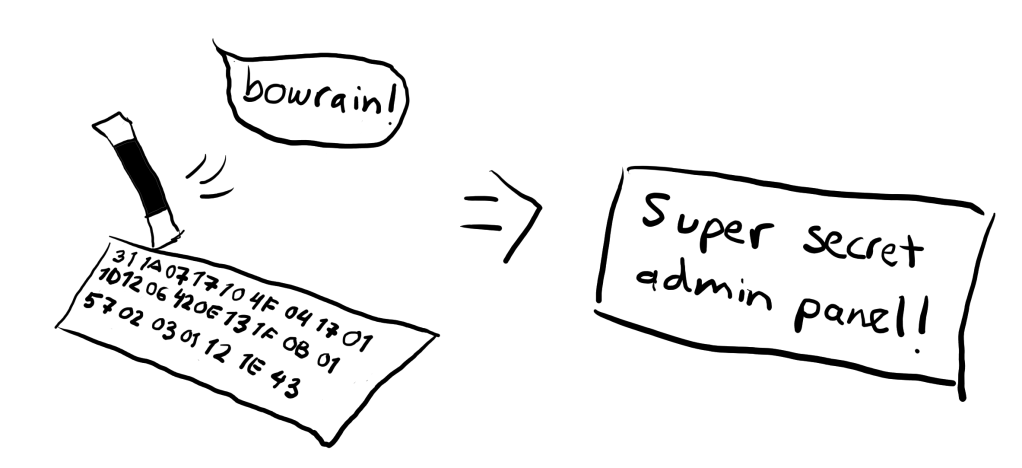
We combine the server’s public key, which was “rain”, with our secret key, “bow”. We tap the message and say the combined word, which clearly is “bowrain” – now the message becomes gibberish.
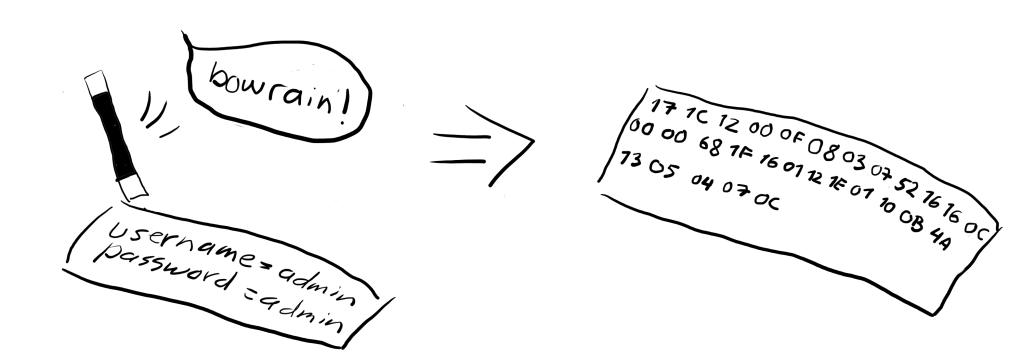
We give this gibberish to the pigeon, along with our public key, “cross” – of course we want to give our public key to the server as well, so that they can use it when they are sending us a message.

The trusty pigeon flies off, with its beak headed for the server. But our pigeon is careless, and again flies into the net set up by the dude. However, this time the dude is left empty handed. They see our public key, and they see a gibberish message – but even though they also happen to own a similar magic wand, they do not know our or the server’s private key, which could be used to turn the gibberish back to normal.
So there is nothing they can do. They let the pigeon go free, message untouched – in the end, they do not want people to know that they are reading the messages.
The pigeon reaches the server. The server now knows our public key, “cross”, which they can combine with their private key, “check”. So, by saying the combined word, which clearly is “checkcross”, they can turn the gibberish back to the original message. They approve our login information, and write us a message which has the private information we requested. They then again use the combined word, “checkcross”, to encrypt the message, before sending the pigeon on its way back to us.
And finally, the pigeon returns with the gibberish message. We tap it, say “bowrain”, and are able to see our private information.
And there we have it – a (huge!) simplification of how HTTPS works.
In this post we have explored the usage of TLS, or Transport Layer Security. TLS is a method of hiding content using encryption. When something is hidden inside TLS, it is said that the content is being tunneled. In this example, we tunneled HTTP traffic. When HTTP traffic is tunneled inside TLS, it is called HTTPS. The magic wand, with the public and private keys, represented public key encryption. Specifically, it depicted Diffie-Hellman key exchange.
Thank you for reading, and see you again next time!
One thought on “HTTPS – a (huge!) simplification”